In the pursuit of total information governance, many organizations focus their security investments on the entry and exit points of the building. They install high-tech RFID file tracking at the registry doorway and implement sophisticated chain of custody tracking at the checkout desk. However, a significant security gap often remains: the “in-between” time.
Once an authorized recipient checks out a sensitive file and carries it into a shared workspace, the file enters a zone of vulnerability. In open-plan offices, busy clinical wards, or collaborative legal environments, staff often leave documents on desks, place them in shared bins, or carry them through public hallways. Without physical protection, even the most advanced digital tracking systems cannot stop someone from removing or tampering with a single page.
At TrackerIoT, we advocate for a layered security approach. By integrating secure file carriers with the IoTFileTracker platform, organizations can ensure that secure file handling extends beyond the file room, providing a physical shield that complements our digital oversight.
The Chain-of-Custody Challenge in Shared Workspaces
Most information security breaches are not the result of a sophisticated external heist; they are the result of opportunity. When a file is removed from a secure file room, the primary security mechanism shifts from facility-grade locks to individual accountability.
Risks in Proximity
In a modern shared workspace, dozens of individuals may have physical proximity to a sensitive file throughout the day. If a records manager or an attorney leaves their desk for a brief meeting, an unsecured folder remains vulnerable. A passerby could inadvertently or intentionally remove a document, browse sensitive data, or misplace a page, and no one would notice until an audit days or weeks later.
The Overlooked Risk of Document Tampering
Tampering doesn’t always involve theft. It can involve the unauthorized copying of a page, the alteration of a signature, or the insertion of a fraudulent document. Standard folders offer no resistance to this. Records management security requires a solution that makes unauthorized access difficult and detectable.
RFID Validation Before and After File Transfers
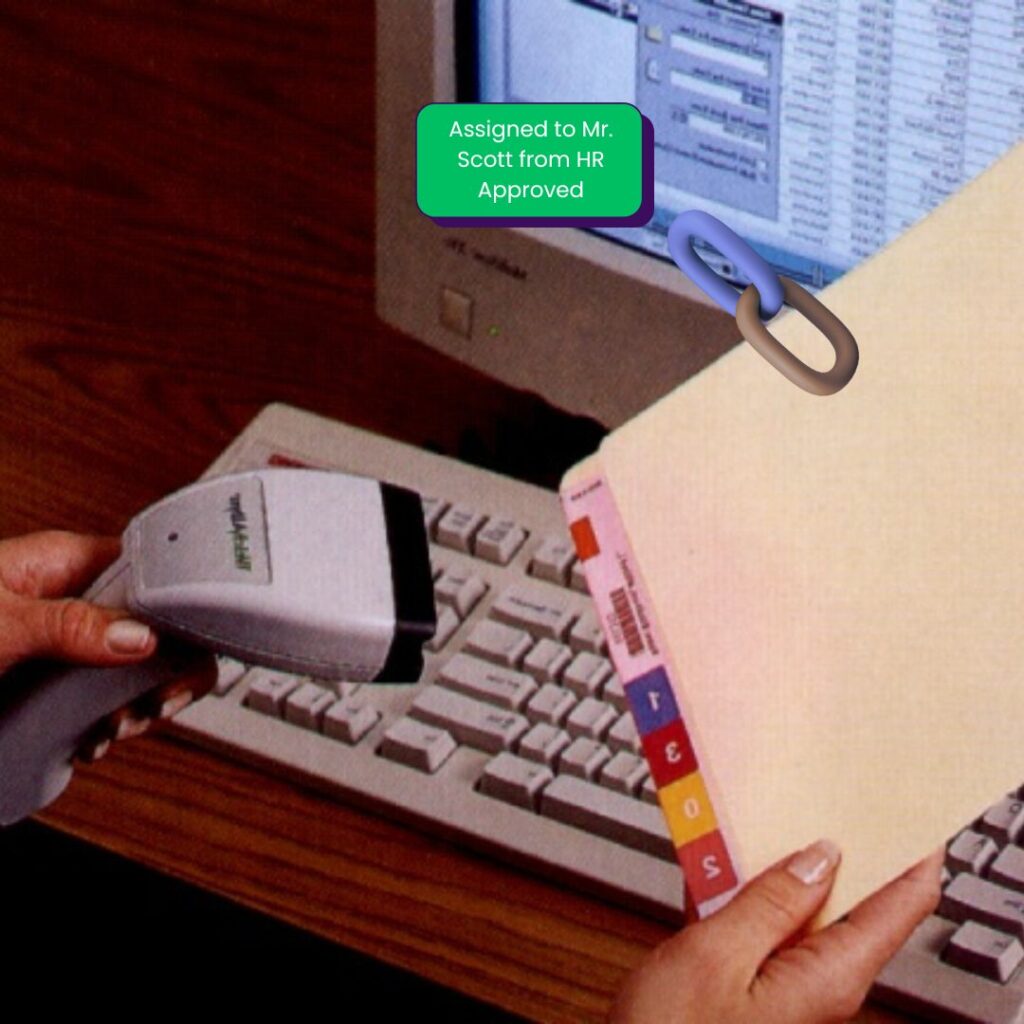

The IoTFileTracker platform provides the digital foundation for secure transfers. Before a file is issued to a recipient, the system performs an automated “Folio Validation.”
Validating Folder Contents
By scanning the folder with an RFID reader, IoTFileTracker verifies that every tagged document—every “child” record—is physically present within the “parent” folder. This ensures the recipient is starting with a complete set of data.
Detecting Missing Documents Upon Return
The same process occurs upon return. If someone checks a file back into the registry and a document is missing, the system flags the error immediately. However, without a secure file carrier, the recipient may claim they have no idea when or how the document disappeared. This “deniability” is a major hurdle in file tracking for compliance. Secure carriers remove that deniability by protecting the file during the custody period.
Why Accountability Alone Is Not Always Enough
Relying solely on an employee’s “responsibility” assumes they have total control over their environment at all times. In reality, documents are often left unattended during lunch breaks, meetings, or overnight.
Accountability tells you who had the file, but it doesn’t always tell you what happened to the file while they had it. When someone removes a document without the custodian’s knowledge, they compromise the chain of custody despite the custodian’s best intentions. Secure file carriers provide the physical barrier that supports the custodian’s accountability in real-world conditions.
What Are Secure File Carriers?
A secure file carrier is a specialized, durable pouch or case designed to house sensitive records during transit and use. Unlike a standard manila folder, these carriers are engineered for physical records security.
Locking, Sealing, and Numbering
Most secure carriers feature:
- Locking Mechanisms: Specialized zippers or hasps that can be secured with a physical lock or a tamper-evident seal.
- Unique Numbering: Every carrier has a permanent serial number that is indexed within IoTFileTracker.
- RFID Integration: The carrier itself often contains an RFID tag, allowing IoTFileTracker to track the carrier and the files inside as a single unit.
How Secure File Carriers Prevent Tampering
The primary goal of a carrier is to provide a “Verified State” for the documents. They prevent tampering through two main avenues:
1. Physical Barriers
A locked or sealed pouch prevents a casual passerby from flipping through a file or pulling out a page. It forces an intruder to commit a deliberate, visible act of destruction (breaking a seal or cutting the pouch) to gain access.
2. Visual and Mechanical Tamper Indicators
If a secure carrier uses a tamper-evident seal, the custodian can immediately see whether someone accessed the file. This creates a psychological deterrent; an unauthorized person is far less likely to touch a file if they know their intrusion will be immediately obvious upon the custodian’s return.
Secure File Carriers and Custody Responsibility
When a file is issued in a secure carrier via IoTFileTracker, the “hand-off” carries more weight. The recipient can see that the seal is intact, confirming that they are receiving a pristine record.
Clear Ownership of Responsibility
By accepting a sealed carrier, the recipient acknowledges that the documents are intact. If they return the carrier with a broken seal or a missing lock, the burden of proof shifts. This strengthens the chain of custody tracking by providing a physical “receipt” of the record’s integrity.
Using Secure File Carriers in Daily Operations
Integrating carriers into a workflow doesn’t have to be cumbersome.
- Internal Transit: When staff move files between floors or buildings, carriers protect them from loss if someone drops or mislays a folder.
- Temporary Unattended Storage: If a worker must leave their desk, they can lock the carrier, ensuring the documents are safe for the duration of their absence.
- The “Pouches-to-Registry” Return: Staff return files to the registry inside their locked carriers, maintaining a “closed-loop” security environment.
Integrating Secure File Carriers with IoTFileTracker
The true power of secure file carriers is realized when they are managed by IoTFileTracker. The software manages the relationship between the carrier and the files.
- Association: When a file is placed in a carrier, IoTFileTracker “parents” the file to that specific carrier ID.
- Audit: A records manager can scan a rack of carriers and instantly know which files are inside each one without opening them.
- Alerts: If an RFID-tagged carrier passes through an unauthorized exit doorway, IoTFileTracker triggers a high-priority alarm, notifying security that a protected asset is leaving the building.
This combination creates a robust secure document storage environment that is both digitally tracked and physically protected.
Chain-of-Custody Benefits for Compliance and Audits
For organizations in highly regulated sectors, the combination of RFID file tracking and secure carriers provides an “audit-ready” posture.
- Reduced Disputes: There is no ambiguity about when a file was accessed or by whom.
- Stronger Accountability: It demonstrates to regulators that the organization has taken “reasonable steps” to protect physical data.
- Proof of Integrity: During a legal or medical audit, you can prove not only that you have the file, but also that you handled it in a tamper-resistant manner throughout its lifecycle.
Future of Secure Physical Records Handling
The future of secure file handling relies on a layered approach that perfectly synchronizes the physical and digital worlds. We anticipate the rise of “Smart Carriers” with electronic locks integrated with IoTFileTracker that open only when an authorized user scans their badge.
By utilizing physical safeguards to complement digital tracking, organizations can achieve a level of security that is greater than the sum of its parts.
The Critical Link in Records Security
In a secure records management strategy, the secure file carrier is the critical link that protects documents during their most vulnerable moments. It turns a passive folder into an active, protected asset.
By choosing IoTFileTracker, you are implementing a system that understands that security doesn’t end at the file room door. We provide the tools to ensure that your records are validated, protected, and fully auditable—every step of the way.