In the high-stakes world of information governance, the file room—or registry—is the heart of an organization’s intellectual and legal property. Whether it houses sensitive government intelligence, patient medical records, or active legal discovery, the physical security of this space is paramount. However, traditional security measures like locked doors and sign-out sheets are often reactive. They tell you someone was there, but they don’t necessarily tell you what left with them.
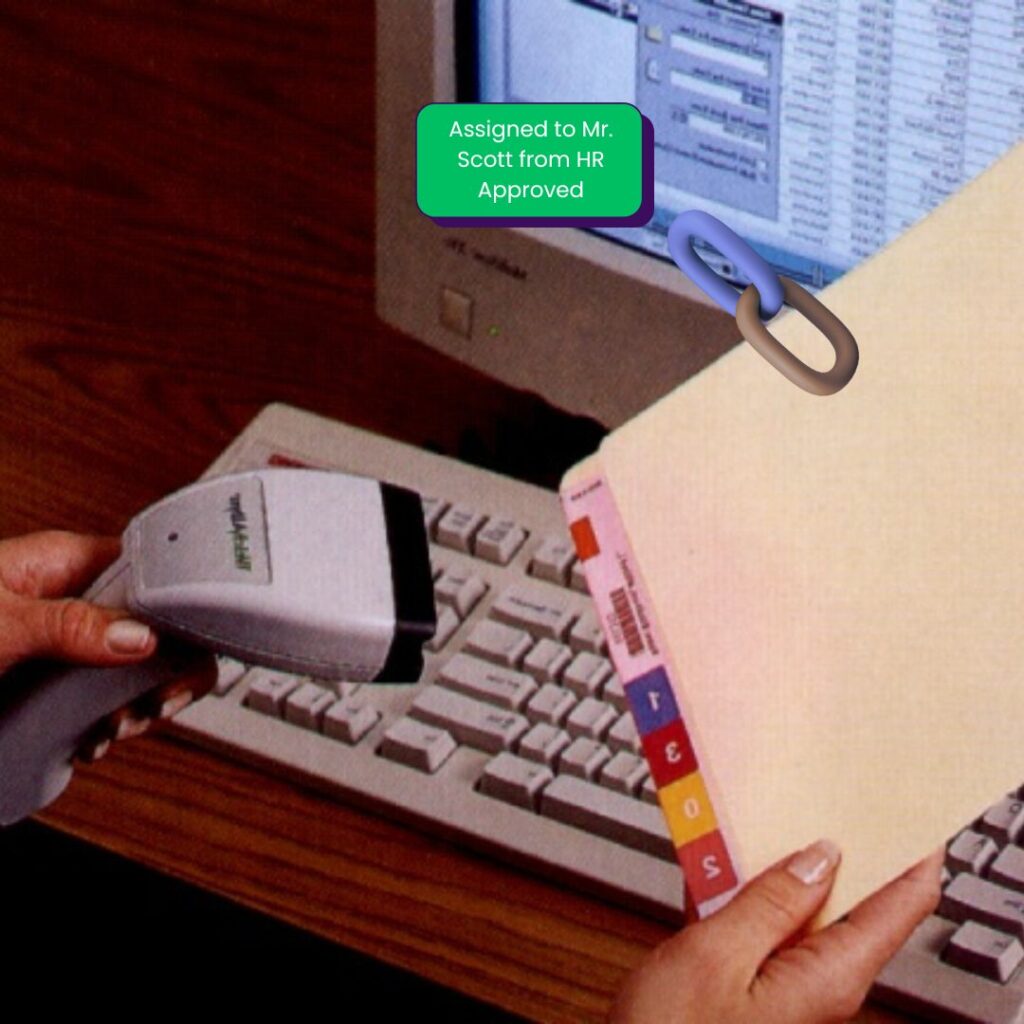
To achieve true records management security, organizations must move toward an active perimeter. By utilizing IoTFileTracker, enterprises can transform standard doorways into intelligent gateways. By integrating RFID technology with sophisticated business logic, IoTFileTracker authorizes, tracks, and audits the movement of every record in real time, effectively eliminating the risk of unauthorized file removal.
Why File Room Security is Critical in Modern Records Management
The modern file room is no longer a passive storage area; it is a dynamic hub of information exchange. As files move between departments, courtrooms, or clinical units, the risk of “information leakage” increases exponentially.
The Risks of Uncontrolled File Movement
Without a robust file room security system, organizations face several critical threats:
- The Accidental Breach: An employee inadvertently carries a sensitive file out of the registry without a proper checkout.
- The Insider Threat: Intentional removal of records for unauthorized use or disclosure.
- Compliance Failure: Regulatory bodies (HIPAA, CJIS, GDPR) require a verifiable chain of custody. A file that “disappears” from a registry without a record of its exit is a direct violation.
In these scenarios, a standard RFID file tracking system might tell you a file is missing during a monthly audit, but registry doorway security tells you the moment it leaves the room.
Understanding Registry and File Room Doorway Security
Registry doorway security refers to the deployment of fixed RFID infrastructure at the entry and exit points of a secure record storage area. While internal tracking manages where a file sits on a shelf, doorway security manages the “transition of state.”
Internal Tracking vs. Controlled Exits
Internal tracking is about inventory management—knowing you have 5,000 files on the shelves. Doorway security is about access control and enforcement. It acts as a digital checkpoint that cross-references the movement of a physical asset against the authorization rules stored in the IoTFileTracker database. If the movement is not “cleared” by the software, the doorway reacts.
RFID Antennas and Motion Sensors at File Room Doorways
The physical foundation of a secure file registry involves the strategic placement of high-gain RFID antennas and infrared motion sensors.
Determining Direction of Travel
A critical component of the IoTFileTracker logic is determining whether a file is entering or exiting the room. By using a “dual-zone” antenna configuration or integrating motion sensors, the system can distinguish between:
- Check-In: A file returning to the registry (a high-integrity event that updates the status to “Available”).
- Unauthorized Exit: A file leaving the room without a prior electronic checkout (a high-risk event that triggers an alarm).
This directional intelligence prevents the system from triggering false alarms when files simply return to their home location.
Business Rules for File Authorization in IoTFileTracker
At the core of the system is the IoTFileTracker business rules engine. This is where administrators define exactly what constitutes an “authorized” movement.
Valid Transfer-of-Custody Requirements
The system can be configured with specific logic:
- Checkout Validation: The system authorizes a file to exit the doorway only if staff scan it at a checkout station and assign it to an authorized recipient within the last X minutes.
- Security Clearance: The system can flag certain “Top Secret” or “Restricted” files and never authorize them to leave the room, regardless of who carries them.
- Identity Sync: The system can require an employee badge scan at the door to “match” the person to the file they are carrying.
Real-Time Alerts and Alarm Responses

When unauthorized file removal is detected at a registry doorway, IoTFileTracker initiates an immediate, multi-layered response to mitigate the risk.
Visual and Audible Deterrents
Local alerts are the first line of defense. The system can trigger:
- Flashing Light Stacks: High-visibility red lights that signal a breach.
- Audible Alarms: Sirens or chimes that alert the registry staff and the person in possession of the file.
Digital Notifications
Simultaneously, the software sends instant notifications via email and SMS to security teams and records managers. These alerts contain the specific file ID, the time of the event, and the specific doorway where the breach occurred.
Network-Connected Alert Devices
One of the strengths of IoTFileTracker is its ability to centralize security visibility. Alert devices (lights and sirens) can be network-connected and placed in strategic locations far from the registry itself, such as:
- The Main Security Desk: Allowing for immediate dispatch of personnel.
- Administrative Offices: Ensuring management is aware of high-risk movements.
- The Registry Supervisor’s Desk: Providing localized control over the storage environment.
This distributed alert network ensures that an unauthorized movement in a basement registry is immediately visible to the entire security apparatus of the organization.
Handling Unauthorized File Exit Events
When a file exits a doorway without authorization, IoTFileTracker does more than just sound an alarm; it changes the “digital state” of the record.
Updating File Status to Alert State
The file is immediately moved into a “Security Alert” status in the database. This status remains until a records manager physically locates the file and clears the alert. This action prevents the record from becoming “lost in the system” and ensures investigators prioritize the event.
Audit Trails and Incident Investigation
Every doorway event is recorded in the IoTFileTracker “Source of Truth.” This provides an immutable chain of custody tracking record that is essential for file tracking for compliance.
Detailed Incident Logs
Each log entry includes:
- Folder ID and Description: Exactly what left the room.
- Location: Which specific doorway was breached.
- Alert Status: The type of alarm triggered.
- Time and Date: Precise to the millisecond.
These logs are invaluable during internal investigations or when demonstrating to external auditors that the organization maintains a “defensible” records management program.
RFID and Video Surveillance Correlation
For a truly modern security posture, IoTFileTracker integrates with video surveillance systems. By matching the RFID alert timestamp with camera footage, security teams can instantly identify the “Person of Interest.”
Instead of searching through hours of video, a supervisor can click on the alert in IoTFileTracker and see a snapshot or clip of exactly who walked through the doorway with the file. This correlation is the ultimate tool for maintaining document accountability.
Advanced Security Integrations
Beyond alarms, IoTFileTracker can serve as a trigger for advanced facility controls:
- Magnetic Door Locks: Automatically locking the door if an unauthorized restricted file is detected approaching.
- Elevator Controls: Preventing the elevator from moving if an unauthorized file is inside the cab.
- Enterprise Security Systems: Feeding data directly into the organization’s Security Operations Center (SOC).
Industries That Require Registry Doorway Security
Government and Classified Records: Ensuring that “Top Secret” folders never leave the registry without an authorized escort and a digital record.
Healthcare and Patient Documentation: Preventing the accidental removal of physical charts, which could lead to significant HIPAA violations.
Legal and Regulatory Environments: Protecting original contracts and discovery binders from leaving the secure legal library.
The Future of File Room Security with IoTFileTracker
As we look toward the future, the convergence of physical and digital security will only deepen. We anticipate a move toward “Self-Auditing Registries,” where the room itself maintains a 24/7 real-time count of all assets and predicts potential security risks based on movement patterns. IoTFileTracker is the foundational platform for this transition, providing the scalability and intelligence needed for the next generation of records governance.
Conclusion
In an era of increasing transparency and accountability, “tracking” is not enough. To protect your organization’s most valuable information assets, you must secure the doorway. Registry doorway security provided by IoTFileTracker ensures that your files are not just organized, but protected.
By enforcing authorization rules at the point of exit and providing a clear, time-stamped audit trail for every movement, we help you maintain total compliance and absolute security.