In the traditional landscape of records management, organizations often focus their resources on the organization and retrieval of documents. However, in an era of heightened regulatory scrutiny and sophisticated insider threats, knowing where a file is “supposed” to be is only half of the security equation. To truly protect sensitive data, organizations must control where that data is allowed to go.
While secure file tracking provides the visibility needed for daily operations, it is the implementation of exit door security that provides the ultimate safeguard against loss. At TrackerIoT, we believe that a robust security posture requires more than just passive monitoring; it requires a proactive system capable of identifying and stopping unauthorized movement in real-time. Through the IoTFileTracker platform, we enable enterprises to turn their physical exits into intelligent security perimeters, effectively eliminating the risk of unauthorized file removal.
The Risk of Unauthorized File Removal
Removing a physical file from a secure facility represents a serious failure in information governance, whether intentional or accidental. Teams can sometimes contain digital breaches through network isolation. A physical file that leaves the building falls completely outside organizational control.
Insider Threats and Accidental Breaches
Most security incidents are not the result of external thefts. Authorized employees often cause them accidentally or through deliberate misuse. Without RFID file security at exits, organizations detect these incidents only during manual audits weeks or months later.
Compliance, Legal, and Reputational Impact
For government agencies, the removal of classified materials is a matter of national security. In healthcare, a missing patient chart is a direct HIPAA violation. For legal firms, losing discovery documents can lead courts to dismiss a case. Beyond the fines, the reputational damage of a public “lost record” incident can be permanent. IoTFileTracker mitigates these risks by ensuring that the facility’s perimeter is as secure as its internal storage.
What Is Exit Door Security in File Tracking?


Exit door security is the application of RFID technology at the boundaries of a secure environment to detect and alert on the movement of tagged assets. While internal secure file tracking might use handheld scanners or “smart shelves” to manage inventory, exit monitoring is a fixed, high-availability infrastructure.
Defining RFID-Based Exit Monitoring
Unlike a standard check-out station, exit monitoring actively detects every tagged file that passes through a doorway, even when the person carrying it does not intend to stop. These “security zones” serve as the final filter in the chain of custody tracking process, ensuring that no document bypasses the mandatory check-out protocols.
How RFID Exit Security Zones Work
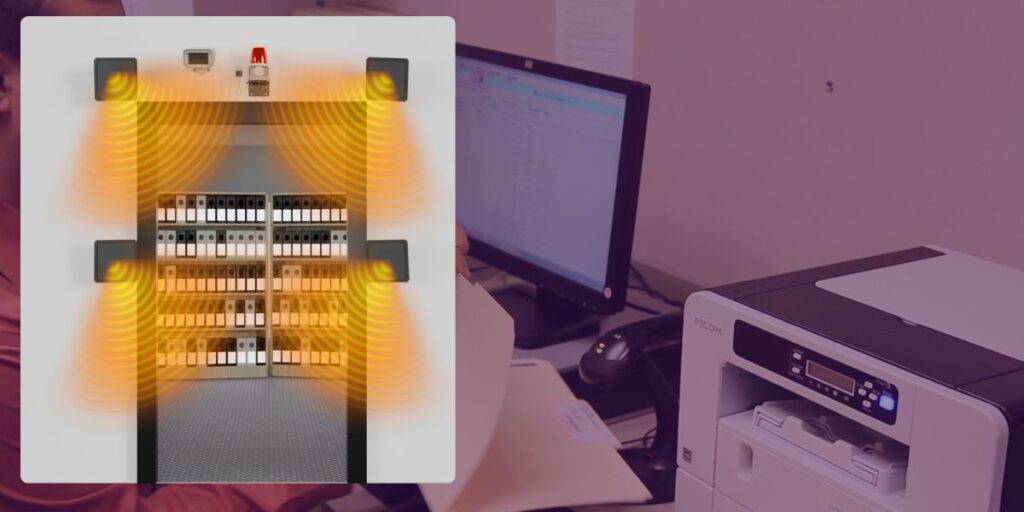
To achieve the high detection rates required for records management security, organizations must optimize the physical installation for the environment. IoTFileTracker leverages high-gain, circular-polarized antennas to detect files regardless of their orientation.
Overhead and Side-Mounted Antennas
Depending on the architectural constraints of the building, antennas mount above the door frame (overhead) or on the sides (pedestal style).
- Overhead Antennas: Ideal for wide corridors and aesthetic-sensitive environments.
- Side-Mounted Antennas: Provide superior detection for files carried close to the body or tucked into bags.
By creating a three-dimensional “read zone” at the exit point, IoTFileTracker captures the unique RFID signal of every folder, binder, or document as it crosses the threshold.
Defining Security Rules in IoTFileTracker
Hardware is only as smart as the software governing it. IoTFileTracker acts as the central intelligence hub where administrators define the “logic” of the exit doors.
Policy-Driven Enforcement
Rather than a “one-size-fits-all” alarm, IoTFileTracker allows for nuanced security rules:
- “No Files May Leave”: Any tagged item crossing the threshold triggers an alarm.
- “Restricted/Classified Only”: Only files with a specific security classification trigger an alert, allowing standard documents to move freely.
- “Authorized Check-Out Exception”: If the system properly checks out a file to an authorized recipient, the exit door allows it to pass without triggering an alarm.
This level of customization ensures that security does not become a bottleneck for legitimate operational workflows.
Real-Time Alerts and Alarms
When the system detects unauthorized file removal, every second counts. IoTFileTracker uses a multi-tiered alert system to ensure teams handle the event immediately.
Visual and Audible Alerts
Local deterrents are the first line of defense. High-visibility LED light stacks (Red/Green) and audible sirens provide an immediate signal to the person carrying the file and to nearby security personnel.
Software, Email, and SMS Notifications
Simultaneously, IoTFileTracker sends digital alerts to administrators. These notifications include the exact file name, the specific door used, and the timestamp. This process logs the incident and reports it to the appropriate chain of command, even when no security officer is present at the door.
Advanced Exit Controls
In high-security environments, IoTFileTracker can go beyond simple alerts to provide active physical containment.
- Triggering Door Locks: The system can be integrated with electromagnetic door locks. If a restricted file is detected approaching a door, the system can automatically lock the door to prevent exit.
- Escalation Workflows: For classified or high-value records, the system can trigger a building-wide lockdown or notify law enforcement automatically.
Securing Stairwells, Elevators, and Shared Buildings
Security threats aren’t limited to the front door. In multi-tenant buildings or large campuses, documents are often at risk during “lateral movement.”
IoTFileTracker allows for the creation of RFID security zones at elevators and stairwell entrances. This ensures that even if a file doesn’t leave the building, you know if it has moved from a secure floor to a public floor. This is essential for file tracking for compliance, as it maintains the integrity of the “secure zone” within a larger facility.
Integrating Video Surveillance with RFID Alerts
One of the most powerful features of the IoTFileTracker ecosystem is the convergence of RFID data with video surveillance. When an exit alarm is triggered, the system can correlate the RFID event with the nearest security camera’s video feed.
Identifying Persons of Interest
By clicking on an alert in the IoTFileTracker dashboard, a security manager can instantly view the video clip of the person passing through the door at that exact second. This eliminates the need to manually scrub through hours of footage and provides definitive proof of who was in possession of the file during the incident.
Chain-of-Custody and Incident Investigation
Every exit alert is an entry in the permanent audit trail. If a file is eventually found missing, IoTFileTracker logs provide a searchable history of every exit approach. This data supports internal investigations and demonstrates to regulators that the organization maintains a rigorous file room security program.
Industries That Require Exit Door File Security
Government and Classified Records: Agencies managing state secrets or sensitive investigative files use IoTFileTracker to ensure that “Top Secret” materials never leave the SCIF (Sensitive Compartmented Information Facility).
Healthcare and Patient Data: Hospitals use exit monitoring to prevent the accidental removal of physical patient charts, protecting the organization from costly HIPAA settlements.
Legal and Regulatory Environments: Law firms and corporate legal departments use these systems to ensure that discovery binders and original contracts stay within the secure confines of the office.
Enterprise Records Centers: Global corporations use RFID file security to protect intellectual property and trade secrets housed in their physical archives.
The Future of RFID-Based Facility Exit Security
As buildings become “smarter,” the integration between IoTFileTracker and facilities management will deepen. We are moving toward a future where “Identity and Asset” are inextricably linked—where a door will only open if both the person’s badge and the file’s RFID tag are authorized to pass together. This integrated physical-digital governance represents the next frontier in records protection.
Conclusion
In the pursuit of total information governance, the exit door is the final point of failure. A file tracking system that only monitors the shelves is incomplete. To achieve true records management security, organizations must secure the perimeter.
IoTFileTracker by TrackerIoT delivers the technology, logic, and auditability needed to prevent unauthorized file removal and enforce compliance. The system protects documents from creation through secure archiving. It also secures every exit point in between.