In the high-stakes environment of enterprise records management, the “Chain of Custody” is the absolute baseline for operational integrity. For government agencies, healthcare systems, and legal firms, the ability to prove who had a specific document at a specific time is not just a matter of convenience—it is a legal and regulatory necessity. Yet, many organizations still rely on antiquated paper sign-out logs that are prone to illegibility, loss, and manipulation.
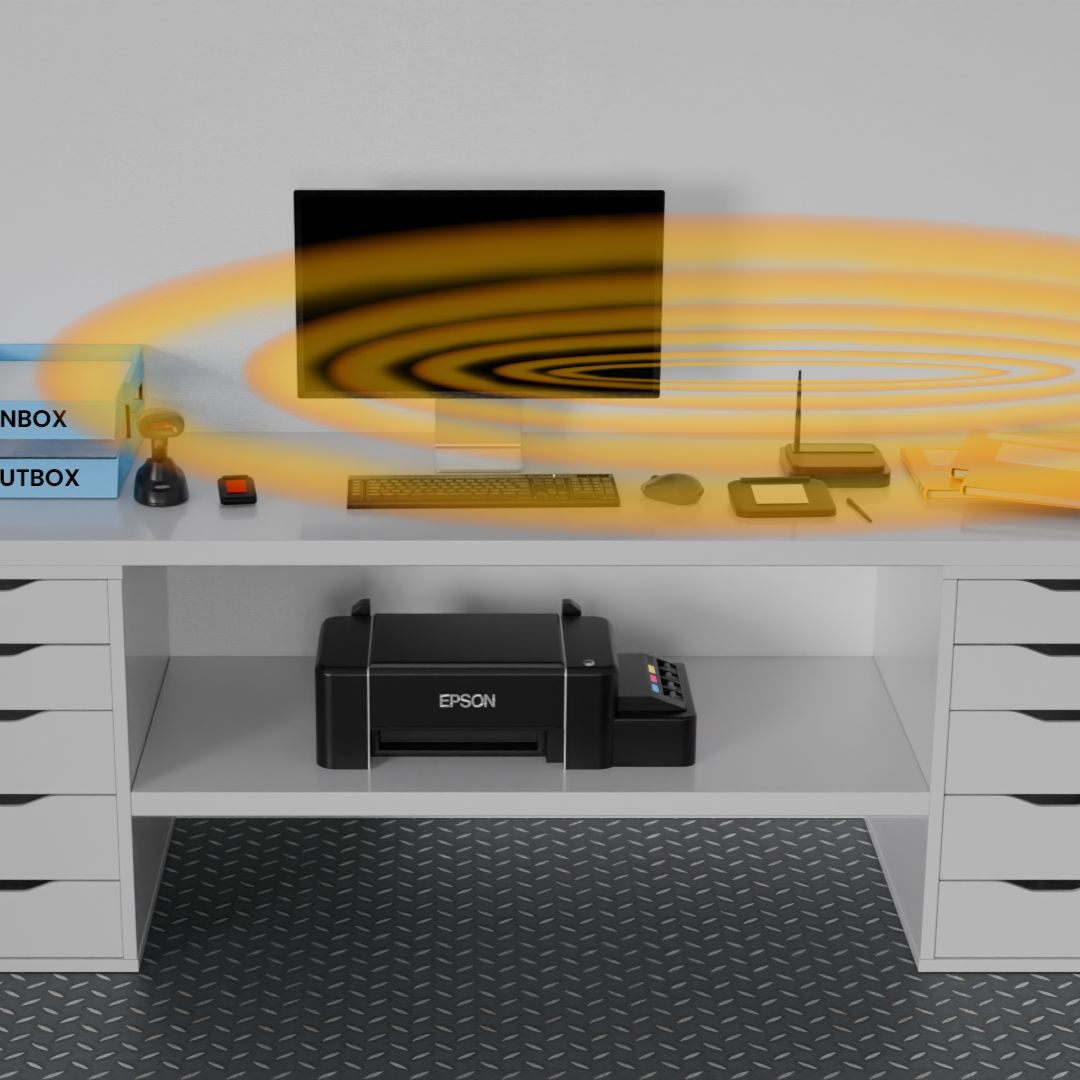
To address these vulnerabilities, modern records centers are transitioning to digital-first workflows. By integrating electronic signatures with the IoTFileTracker platform, organizations can transform a simple file hand-off into a secure, immutable, and fully auditable event. This synergy of hardware and software ensures that every chain-of-custody tracking event is backed by a “digital handshake” that enforces total accountability and records management security.
What Is Chain-of-Custody in Records Management?
Chain-of-custody refers to the chronological documentation or paper trail that records the sequence of custody, control, transfer, and analysis of physical or electronic evidence. In the context of physical records management, it is the unbreakable link between a folder and the human being responsible for it.
Legal and Compliance Implications
When a record is needed for a court case, a medical audit, or a financial review, the first question asked is often: Can you prove the integrity of this document from the moment it was created? If the chain-of-custody is broken—meaning there is a gap in the timeline of who held the file—the document may be deemed inadmissible or untrustworthy. IoTFileTracker ensures that this gap never exists by creating a permanent, searchable record of every custody transfer.
Limitations of Manual Signatures and Registry Books
Traditional paper registry books have been the standard for decades, but they represent a significant point of failure in a modern compliance framework.
- Human Error: It is easy for a staff member to forget to sign a book during a busy shift, creating a “black hole” in the file’s history.
- Illegibility: Handwritten signatures are often impossible to decipher months or years later, rendering the audit trail useless.
- Lack of Real-Time Visibility: A paper log only exists in one physical location. If a manager in a different department needs to know who has a file, they have to physically travel to the file room to check the book.
By replacing these books with a digital file tracking system, organizations move from a reactive search model to a proactive governance model.
What Are Electronic Signatures for File Custody?

Electronic signatures in a records management context are digital acknowledgments of a transfer of responsibility. When a file is issued via IoTFileTracker, the recipient signs an electronic pad or enters a unique credential. This signature is then cryptographically linked to the specific file’s RFID tag and the exact timestamp of the transaction.
Manual vs. Electronic Custody Validation
While a manual signature is a static mark on a piece of paper, an electronic signature within IoTFileTracker is a data-rich event. It doesn’t just record a “name”; it records the user ID, the location of the transfer, the specific files included in the batch, and the current status of those files. This provides a level of digital chain-of-custody that paper simply cannot match.
How Electronic Signatures Improve Accountability
The primary goal of any records management compliance strategy is non-repudiation—the inability of a person to deny their involvement in a transaction.
Clear Proof of Custody
When a staff member provides an electronic signature, they are taking formal, recorded responsibility for that asset. This psychological and digital “weight” significantly reduces the likelihood of files being left in unsecured areas or passed to unauthorized colleagues without a formal transfer.
Time- and Date-Stamped Verification
Every signature in IoTFileTracker is automatically time-stamped by the system clock. This eliminates the risk of “back-dating” or “forward-dating” that can occur with manual logs, ensuring that the audit trail reporting is accurate to the second.

Capturing Electronic Signatures During File Transfers
The IoTFileTracker workflow is designed to be operationally practical, fitting into the natural rhythm of a busy file room or registry.
File Issuance Workflows
When a user requests a file, the records manager pulls the folder and scans its RFID file tracking tag. The system identifies the file and prompts the recipient to sign the electronic pad. Once the signature is captured, the file’s status is instantly updated from “In File Room” to “Out to [User Name].”
File Return Workflows
The process is equally rigorous during returns. The folder is scanned, the return is acknowledged, and the system can be configured to require a “return signature” or a supervisor’s verification to confirm that the file was returned in its entirety and in good condition.
Building a Digital Chain-of-Custody Record
The true power of IoTFileTracker lies in its ability to aggregate these individual signatures into a comprehensive history.
Viewing and Printing Custody Reports
Administrators can query any file and see its entire “life story.” The system generates a report showing every person who has ever held the file, the duration of their custody, and the signatures associated with each transfer. These reports can be exported as PDFs or printed for physical evidence binders, providing physical records security through total transparency.
Audit Trails and Compliance Readiness
For organizations subject to HIPAA, CJIS, or Sarbanes-Oxley, audit readiness is a constant requirement. IoTFileTracker makes this process frictionless.
- Internal Audits: Managers can run weekly reports to identify files that have been checked out for too long or to verify that all transfers have been properly signed for.
- Regulatory Inquiries: When an auditor asks for the history of a specific sensitive record, IoTFileTracker provides a complete, verified digital record in seconds, rather than requiring hours of manual labor to find and photocopy paper logs.
Advanced Authentication Options
For high-security environments, IoTFileTracker supports more than just basic signature pads.
- PIN-Based Validation: Users must enter a unique PIN to authorize the custody transfer.
- Biometric Verification: Integration with fingerprint or iris scanners ensures that the person taking the file is exactly who they claim to be. This level of records management security is essential for classified government records or high-value intellectual property.
Integrating Electronic Signatures with RFID File Tracking
The most robust security model combines “Who” (Electronic Signatures) with “Where” (RFID file tracking).
By integrating these two technologies, IoTFileTracker can verify custody and location simultaneously. For example, if a file is detected by an exit doorway antenna but no “Authorized for Removal” signature was recorded, the system can trigger an immediate alarm. This reduces disputes and provides an airtight layer of protection against unauthorized file removal.
Operational and Security Benefits
Faster File Transfers
Automated digital signatures eliminate the bottleneck of looking for the right page in a logbook or finding a working pen. Transfers happen in seconds, improving file transfer accountability without slowing down staff.
Improved Confidence in Records Integrity
When stakeholders know that every movement of a file is electronically verified, their confidence in the data increases. This is particularly vital in legal and healthcare settings where the document is the basis for critical decisions.
Industries That Benefit Most
- Government: Ensuring that sensitive citizen data and investigative files are handled only by authorized personnel.
- Healthcare: Maintaining strict HIPAA compliance by tracking the movement of patient charts (PHI).
- Legal: Protecting the attorney-client privilege by ensuring a perfect chain-of-custody for discovery materials and evidence.
- Financial Services: Managing original loan documents and contracts with high-fidelity audit trails.
Best Practices for Implementing Electronic Signatures
To ensure success, TrackerIoT recommends the following steps:
- Define Custody Policies: Clearly state which types of files require a signature and who is authorized to take them.
- Training Staff: Ensure that everyone understands that the electronic signature is a formal legal acknowledgment of custody.
- Align Technology with Workflows: Place signature pads at logical transfer points, such as the registry counter or departmental intake desks.
Conclusion
In the pursuit of total compliance and operational efficiency, “good enough” tracking is no longer an option. Electronic signatures provide the definitive proof of possession that manual systems lack, creating a culture of accountability within your organization.
By choosing IoTFileTracker, you are not just buying a software platform; you are implementing a sophisticated security framework that protects your records, your staff, and your reputation. TrackerIoT is your partner in building a future where physical records are as secure, searchable, and auditable as their digital counterparts.