In the current landscape of information governance, the stakes for physical document management have never been higher. While digital cybersecurity often dominates the headlines, the physical records that sit in government archives, hospital basements, and law firm storage rooms remain significant vulnerabilities. For organizations handling sensitive data, simply knowing where a file is “supposed” to be is no longer sufficient. True document and file security requires a proactive, layered approach that monitors movement, validates authorization, and enforces accountability in real-time.
At TrackerIoT, we recognize that a modern file security system must do more than just index records; it must protect them. Through our IoTFileTracker platform, we bridge the gap between simple location tracking and comprehensive security, providing the tools necessary to prevent data breaches before they occur.
The Modern Challenge of Document and File Security
Traditional records management relies heavily on the “honor system” or manual sign-out sheets. These processes are fundamentally flawed because they are reactive. By the time a records manager realizes a file is missing, they have often lost the opportunity to recover it, and a potential compliance violation has already occurred.
Visibility Gaps and Insider Risk
Most document losses are not the result of external thefts but rather “insider risk”—the accidental or intentional mishandling of files by authorized personnel. Without secure records management, organizations cannot verify whether someone left a file in an unsecured area, took it home, or handed it to an unauthorized colleague. This lack of visibility creates a massive blind spot for Compliance Officers and CIOs.
File Location vs. File Security: Understanding the Difference
It is critical to distinguish between tracking and security. RFID file tracking tells you that a file moved from Room A to Room B. Document and file security, however, asks: Is the person moving this file authorized to do so? Is Room B a secure location for this classification of data? Has the file been away from its home for too long?
IoTFileTracker layers security logic on top of RFID data. It transforms passive location pings into actionable intelligence, ensuring that every movement aligns with the organization’s security policies.
Validating Documents Inside File Folders
A secure folder is only as good as its contents. One of the most common security failures happens when someone removes individual documents from a folder or misfiles them into another one.
IoTFileTracker supports item-level tagging. By applying discreet RFID tags to individual high-value documents within a folder, the system can perform a “Folder Integrity Check.” When a folder is scanned, the software verifies that all required documents are present. If a critical contract or medical record is missing from the folder, the system triggers an immediate alert, preventing the “hollow folder” syndrome that plagues many manual systems.
Secure File Transfers and Custody Validation
The “Chain of Custody” is the backbone of file tracking for compliance. In a secure environment, every transfer of a file from one person to another must be a deliberate, recorded event.

Enforcing Chain of Custody
IoTFileTracker digitizes the transfer process. When someone checks out a file, the system records the requester’s identity and the transaction time. If the file moves to another department, the system enforces a “handshake” validation. This ensures that the chain of custody remains unbroken and that there is never a moment when a file’s “current custodian” is unknown.
Authorized Access Control
Not all employees are entitled to see all records. IoTFileTracker integrates with your organization’s existing identity management systems (such as Active Directory or HID badges) to enforce role-based access control.
When a user pulls a file from the shelf, the system cross-references the file’s security level with the user’s authorization. If an unauthorized individual attempts to remove a sensitive file from a secure file room, the system can lock electronic gates or notify security personnel instantly.
Electronic Signatures and Receipt-of-Custody
To move beyond the deniability of manual logs, IoTFileTracker incorporates digital proof of possession. Upon receiving a file, the recipient can provide an electronic signature via a mobile device or a dedicated workstation.
This digital “receipt-of-custody” creates an immutable audit trail. In the event of an investigation, the records manager can provide definitive proof of who last had physical control of the document, fostering a culture of accountability across the enterprise.
Preventing Unauthorized File Removal
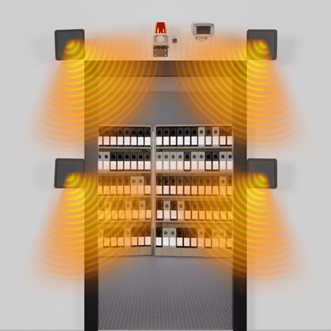
The most critical moment in RFID document security is the exit point. IoTFileTracker utilizes RFID detection zones at doorways and elevators to act as a digital perimeter.
Real-Time Alerts and Escalation
If a file tagged with an RFID inlay passes through a restricted exit without being checked out, IoTFileTracker initiates a multi-stage escalation:
- Audible/Visual Alarm: An immediate local deterrent at the doorway.
- Instant Notifications: Push notifications sent to security via SMS or email.
- Software Logging: The event is flagged in the central dashboard for immediate follow-up.
This proactive unauthorized file removal prevention ensures that files do not leave the facility—or even specific secure zones—without a valid reason.
Secure File Transport
Files are often most vulnerable when they are in transit between buildings or being sent to off-site storage. IoTFileTracker supports the use of “Smart Carriers”—locked bins or bags equipped with their own RFID sensors. These carriers ensure that the documents inside remain protected from prying eyes and accidental loss during the transport phase.
RFID with Video Reconciliation for Investigations
When a security breach occurs, speed of investigation is paramount. IoTFileTracker can be integrated with your facility’s Video Management System (VMS).
When the system triggers an unauthorized removal alert, the software correlates the RFID timestamp with the nearest security camera. This allows investigators to instantly view the footage of the person of interest carrying the file. This convergence of physical RFID data and video evidence provides a level of records management security that traditional systems simply cannot match.
Industries That Require Advanced File Security
Government and Public Records
Government agencies use IoTFileTracker to protect classified intelligence and sensitive citizen data, ensuring that a misplaced folder never compromises national security or privacy.
Healthcare and Patient Data
HIPAA compliance requires strict controls over who can access physical Protected Health Information (PHI). Our system provides the audit trails necessary to satisfy the most stringent healthcare audits.
Legal and Regulatory Environments
Law firms and corporate legal departments use IoTFileTracker to protect client-attorney privilege materials and ensure that only authorized team members handle case files.
The Future of Secure Records Management
The future of document security lies in the “Self-Protecting File.” As IoT sensors become more ubiquitous, we will see environments where files can communicate their status autonomously. IoTFileTracker is at the forefront of this evolution, moving toward integrated physical-digital security where the lifecycle of a document is protected from the moment of its creation to its final, certified destruction.
Conclusion: Proactive Protection with IoTFileTracker
In an era of increasing regulatory pressure and heightening security threats, “tracking” is merely the baseline. To truly protect your organization’s intellectual property and sensitive data, you must implement a system that prioritizes security and accountability.
IoTFileTracker by TrackerIoT provides a comprehensive, security-first framework for the modern enterprise. By automating the chain of custody and enforcing access controls, we turn your file room into a fortress of information governance.